IBM AIX Power systems are enterprise-class open standards-based Unix servers that support critical applications and database workloads having high I/O and memory requirements, and require maximum performance, availability, security and scalability. IBM’s AIX Power systems have been the most popular Unix server line in the world for over a decade for a number of compounding reasons. As a whole, IBM’s AIX Power server platform has countless industry leading benchmarks and application specific achievements that attrct businesses for specific uses cases, but after factoring in software license costs, the total cost of ownership numbers makes the IBM Power platform the obvious choice....
SFTP client software or Secure FTP that uses SSH (Secure Shell) and PGP encryption for secure file transfer over the SSH2 protocol as defined by the Internet Engineering Task Force (IETF) SSH (SECSH) working group. Customers with an AS400, iSeries or IBM i can use the Secure FTP (SFTP) to automate secure file transfers to their bank or other trading partners in just a few minutes. Banks like Bank of America, BankOne, CitiGroup, JP Morgan Chase, State Street, US Bank, Vanguard and Wells Fargo have additional file transfer requirements such as PGP encryption, ASCII armored, RSA public key exchange, sign and verify, key...
IBM Linux server hardware performance and software license costsThe best Linux server hardware for enterprise open-source ecosystems will be the platform that delivers the best processor, memory and disk performance per core. Judging by the number of discussions in customer support communities, technical articles and blog posts on various Linux server performance troubleshooting, there is clearly a need for a better performing Linux server for both scale up and scale out infrastructures. This article will explain the importance of selecting the best performing hardware for your Linux server farm and how it affects software license costs. IBM POWER10 and IBM POWER9 Linux...
We said good bye today to a very dear friend and family member Henry Rodriguez. It was a beautiful ceremony for a truly beautiful person. Henry was loved by everyone that knew him, which showed by the huge turnout. People flew in and drove to Florida from all over the country. Those that had the opportunity to stand up to speak about him, knew exactly what to say. Even if I were asked to speak, I do not know how I would have gotten through it. The entire place had to be tears after hearing his sweet little daughter Oliva speak...
Endpoint security management might be best handled by a Managed Security Service Provider (MSSP) to monitor and manage, because over 70% of cybersecurity breaches originate from endpoint devices, and almost every company admits they lack the required resources. Our endpoint security management services provide a centralized monitoring and remediation service that proactively discovers device vulnerabilities using real-time cybersecurity AI, monitors for required services needed for protection, blocks malicious applications and ensures endpoints are up to date with required patches according to defined policies. Hackers know endpoints are the easiest way to penetrate a network, and companies’ seldomly have multiple security controls...
Is it the right time for you to get a small business server? While the process of growth within small businesses can be exciting, business owners are often faced with technology pains that accompany a growing team. With more people come more computers and the once effective peer-to-peer method of managing computers when there were just a handful of people no longer proves to be effective or sustainable. With this growth in your business, it may be time to consider getting a small business server. If you are beginning to manage a small fleet of computers that share printers, scanners, internet...
IBM recently introduced their newest POWER servers with the POWER9 processor to the marketplace. Has your business has been debating staying on the IBM i platform instead of migrating your data to the cloud or to another OS platform like Linux Servers or another x86 server solution? You really should consider the benefits of the latest POWER9 systems are and IBM i 7.4. The AS400 iSeries POWER lineup of servers has long held a reputation for reliability and security. IBM i is all about integration and innovation. Businesses running high-traffic, mission-critical applications are deploying IBM Systems in their own data centers and in...
The IBM z mainframe system remains the workhorse for most of the largest and most successful companies in the world, maintaining both mission critical legacy software applications and new workloads. In the scope of sensitive data and security, the IBM z/OS protects the company’s jewels for good reason, but has a plethora of system and security event log sources that must be monitored and forwarded to a SIEM like IBM QRadar, AlienVault, Exabeam, Managed SIEM or a SYSLOG Server like the Splunk. Since IBM mainframe event logs do not conform to SIEM and SYSLOG industry standards, many IBM z shops are running batch...
Details of each POWER9 and POWER8 hardware enhancement provided by the release of IBM 7.4 (V7R4) are below the initial summary, organized by IBM Power generation and topic. The new IBM POWER9 and POWER8 hardware features provided for OS400 V7R4 are now all available for ordering as of June 21, 2019. Read about IBM i 7.4 (V7R4) announcement details here. IBM V7R4 announcement provides the following I/O enhancements for Power9 scale-out and scale-up system models: 1.6 TB, 3.2 TB, and 6.4 TB PCIe3 Enterprise SSD NVMe adapters for Power9 E980, E950, L922, S922, S914, S924, H922, and H924 servers1.6 TB and...
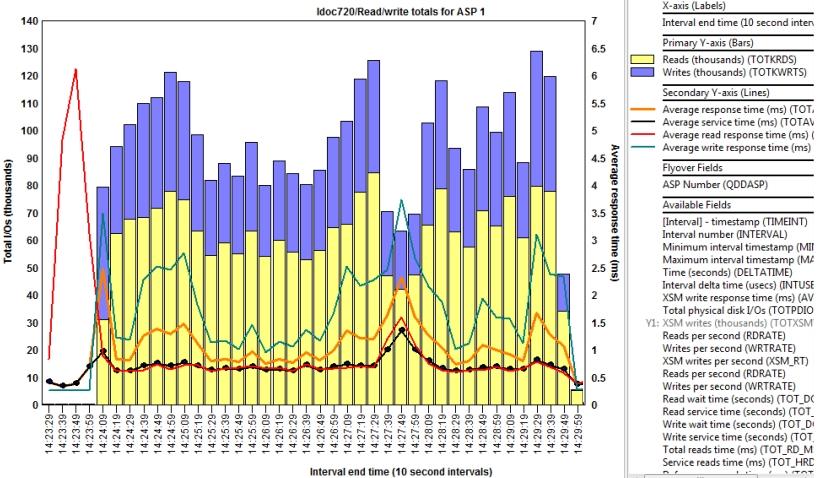
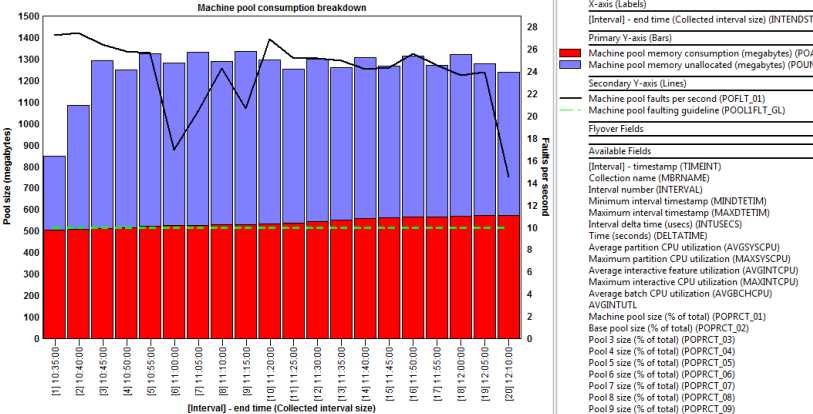
Keeping your IBM i optimized for optimal response times requires regular monitoring of system resources and identifying various elements that affect application performance. Poor response times of only two or three seconds delay can quickly get compounded over time when poorly written applications are involved or database maintenance has been neglected. Like most performance degradation issues on the IBM i, response time issues only get worse as the number of transactions multiply. Ignoring system performance issues affects productivity and frustrate customers, which in turn increases costs and affects revenue. Below are some ideas to consider if a major IBM i upgrade...
IBM EJ14 PCIe3 12 GB Cache RAID Plus SAS Adapter is the highest performing raid controller (SAS adapter) for IBM Power9 and Power8 systems that will significantly improve raid performance. The IBM EJ14 PCIe3 12 GB Cache RAID PLUS SAS Adapter has four 6 Gb connectors enabling the highest performance HDD or SSD SAS controller capabilities for IBM Power systems using PCIe Gen3 technology and IBM’s latest SAS RAID adapter technology. The EJ14 PCIe3 SAS adapter builds on the success of the EJ0L PCIe3 12 GB Cache RAID SAS Adapters, but delivers up to 100% more write IOPs than the older EJ0L...
Is it time to upgrade your IBM i Power System? Or do you need to upgrade your IBM i Power System? Most companies upgrade their IBM Power systems on a scheduled interval, but there are instances when response times and throughput bottlenecks cause unacceptable performance levels, and a quick fix is needed. IBM i response times and throughput rely on common system resources and can have a similar effect on performance from an end user experience, but the variables that cause them are very different and are often difficult to figure out. IBM Power system processors, memory, SSD, disk drives...
Sporadic IBM i performance issues and prolonged degradation that slowly creeps up over time can sometimes be abated by fine tuning memory pools, disk, database, applicatons, jobs and threads, but it’s not a task an untrained administrator should be attempting. IBM i response times and throughput performance issues can be due to numerous factors, and often requires a lot of man hours to pin point by a trained expert. If your IBM Power iSeries already has the Performance Adjuster enabled (view QPFRADJ system value) and other dynamic performance optimization features enabled, it often makes economic sense to simply add memory, disk drives...
Written by: Bob PiccianoOpen any business publication or digital journal today, and you will read about the promise of AI, known as artificial or augmented intelligence, and how it will transform your business. The fact is, AI will not only transform your entire business, whether you are in health care, finance, retail or manufacturing, but it will also transform technology itself. The essential task of information technology (IT), and how we measure its value, has reached an inflection point. It’s no longer just about process automation and codifying business logic. Instead, insight is the new currency, and the speed with which...
Database clustering involves database replication to achieve high availability (mirroring, redundancy and disaster recovery), workload balancing for performance or scaling (queries, reporting, business intelligence, analytics and data warehousing), maintenance (upgrades, migration, testing and development), database consolidation and other objectives for data access, efficiency and better decision making. It is use database clustering and replication services where the source and target databases are at different version levels and even different types of databases all together, such as PostgreSQl to Oracle replication, or DB2 to SQL. Database clustering can be implemented for a mix of on premise, virtual and cloud environments, using any...
Database migration and conversion projects can be a time consuming and costly endeavor without the right software, and converting large complex production databases with real-time replication and transformation requirements significantly compound the risks. Using a database migration and conversion tool to map fields of disparate databases correctly and keeping them in sync is key to a successful and non-disruptive conversion. Critical business applications utilizing the database to be converted will add risk to the migration process. Traditional database migration and database converter processes usually take hours or days for large databases, costing businesses unnecessary downtime. Some companies have wasted millions of dollars in...